Violence is a complex and multifaceted issue that has been the subject of much debate and discussion for centuries. One of the main questions that has emerged in this debate is whether violence is primarily the result of nature or nurture. In other words, is violence something that is innate and inherent in human nature, or is it a product of the environment and the experiences that individuals have throughout their lives?
There is evidence to support both sides of this debate. On the one hand, some research suggests that violence may be genetically influenced and therefore part of human nature. For example, studies have found that individuals who are prone to aggression and violence may have certain genetic variations that make them more likely to engage in aggressive behavior. Additionally, certain hormones, such as testosterone, have been linked to aggressive behavior, suggesting that there may be a biological basis for violence.
On the other hand, there is also a significant body of evidence that suggests that violence is primarily the result of nurture, or environmental factors. For instance, research has shown that individuals who are exposed to violence or aggression in their environment, such as through media or in their home or community, are more likely to engage in violent behavior themselves. Additionally, social and cultural factors, such as poverty, unemployment, and discrimination, have been linked to an increased likelihood of violence.
Overall, it is likely that both nature and nurture play a role in the development of violent behavior. While there may be certain genetic and biological factors that make some individuals more prone to violence, it is also clear that the environment plays a significant role in shaping an individual's behavior. It is important to recognize the complex interplay between nature and nurture in order to effectively address and prevent violence.
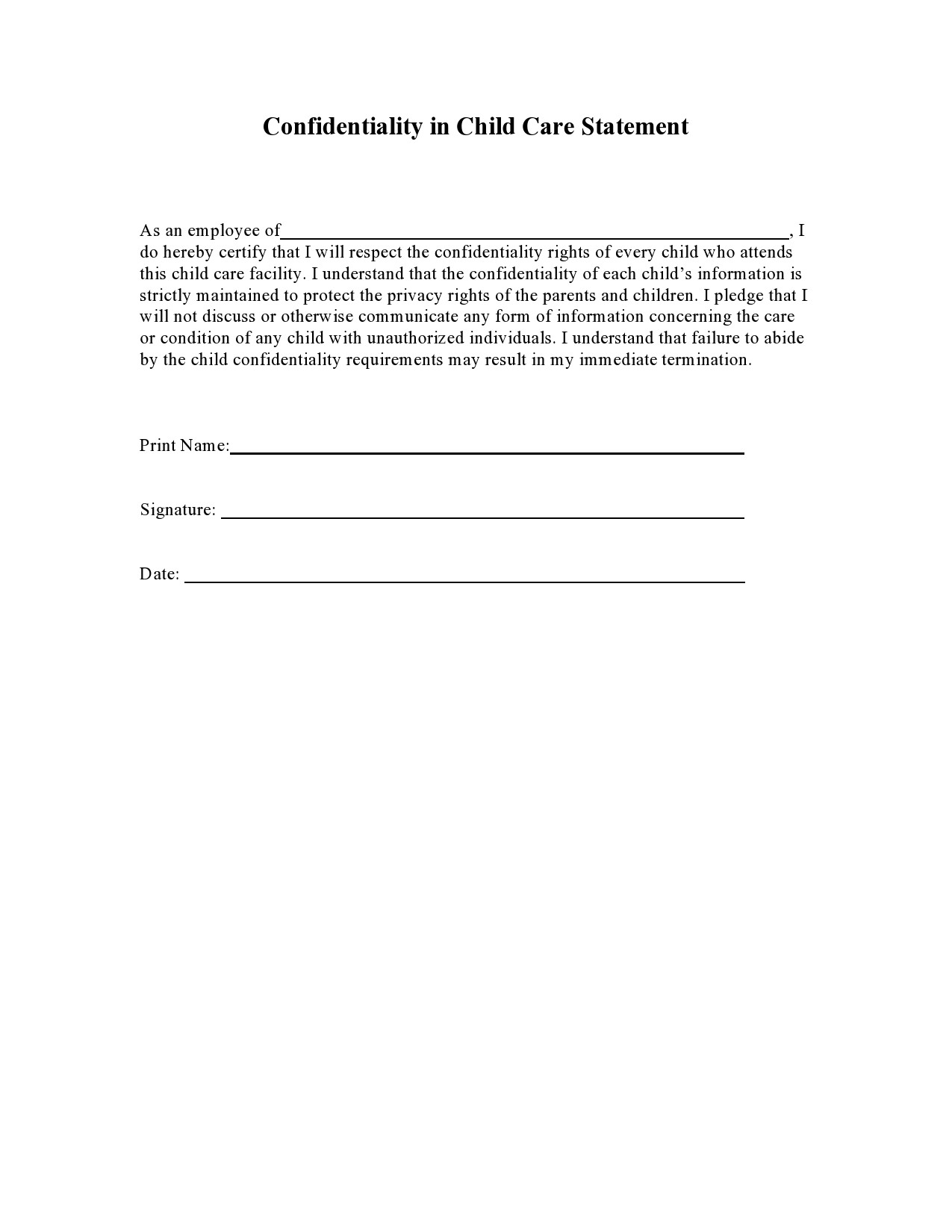
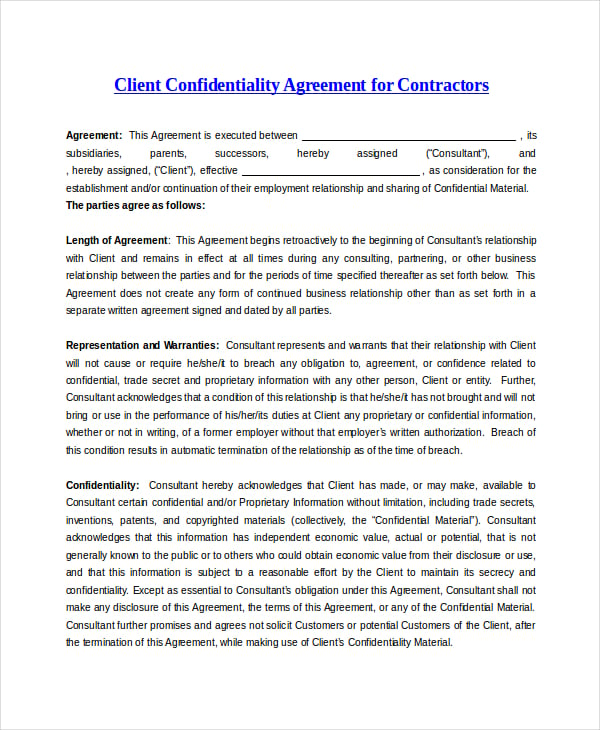
Statement of Confidentiality

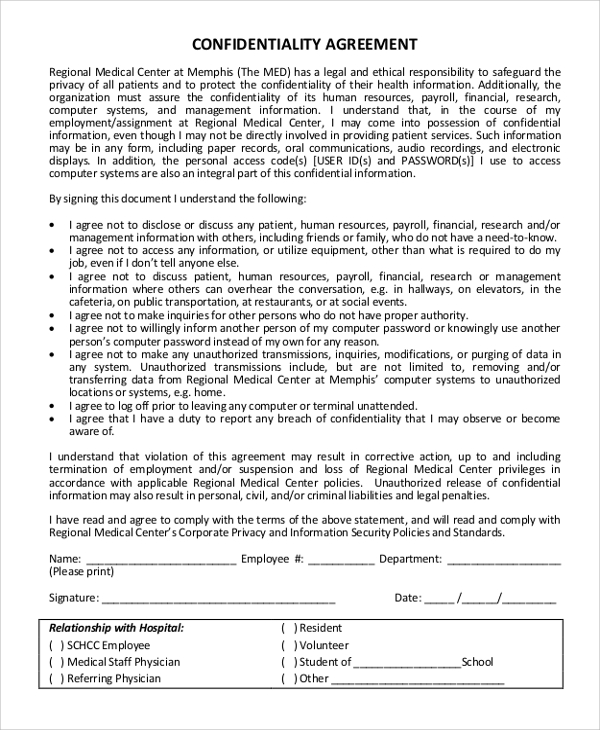
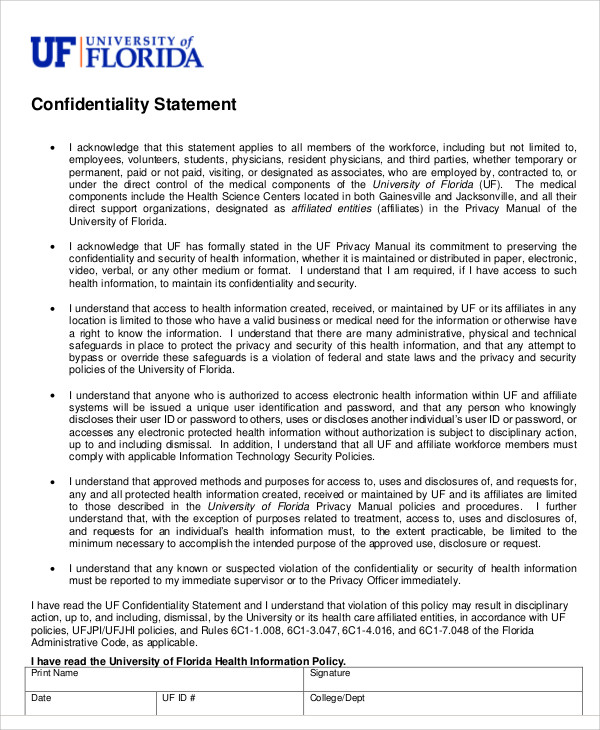
Exclusions from confidential information A confidentiality statement should specify any exclusions from confidentiality and describe how the receiving party can disclose the confidential information. This network type allows employees to interact seamlessly in the office setting while on stationary locations and on the move. TEKLA SOLUTIONS OPERATIONS MANAGER JUSTIFICATION REPORT ON THE NEED TO IMPLEMENT ADVANCED SECURITY FEATURES TO PREVENT COMPANY INFORMATION INTRODUCTION I intend to dedicate this report to Tekla Solutions where the security of the business will be the main focus in securing the safety of business data. Obviously, it requires the signature of all parties before the agreement becomes valid. We will be glad to provide you with an itemized receipt that you can submit to your insurance company in an attempt to receive reimbursement from them. That promise, however, does not mean that change will be easy, or that trusting him will make our lives better.
Confidentiality Report Examples That Really Inspire

With enhanced security, the integrity, confidentiality and availability of information stored in company information systems will be preserved. Such an agreement is primarily designed to be used by a person with data that they wish to protect but disclose to another person. This type of agreement can also be used by inventors seeking help with their inventions. Usually, these brands and middlemen get away with the bulk of the profits leaving very little profits and margin for the original farmers and producers of the goods and services who have contributed to the production process. It borders Oman and Saudi Arabia. Business Ethics Introduction Since the late 20th century, the number of illegal immigrants entering America and other countries has risen sharply. Elements of Healthcare Maintaining Health Records In any health facility, it is necessary to have policies that make necessitate the keeping of medical records.
Confidentiality Statement Example
Introduction Information security is an important part of managing organizations that aims to establish a strong e-commerce presence whether they may be a commercial, government, or not-for-profit organization. In addition, sometimes misunderstandings can inadvertently result in hurt feelings. This may have long-term implications for the nation. They may also be required to return copies given to them or destroy them after a specified period. In this report, the structural development patterns are shown during several periods, which brought tremendous shifts in economic, agricultural and industrial sphere making India the global leader in numerous aspects. If the receiving party breaches the confidential agreement, then the disclosing party is entitled to have its remedy at law in equity. Among them a prominent place is occupied by the United Arab Emirates the UAE that is a country that having faced with many challenges managed to outrun other countries in the region by a number of social and economic indicators.
20+ Confidentiality Statement & Agreement Templates ᐅ DocFormats
These agreements bind the involved parties to specific responsibilities regarding the disclosure of confidential information. . Design-Bid-Build: - Firstly, an engineering design firm is contracted to establish guidelines on the required materials, equipment and the potential costs to complete the project. . Protection of merger plans and information — a great deal of information is shared between companies to assist in the evaluation of whether the merger should proceed, whether it makes sense for both companies, and to provide a valuation of the merger. Disclosure of information may be restricted to the entire company or specific individuals within the company.
16 Basic Confidentiality Statement Examples [Free Templates]
. With Focus on the Privacy Act 1988, the Freedom of Information Act 1989 and the Anti-Discrimination Act 1977 In Australia, other than the laws passed by the parliament of Australia which apply to all states and mainland territories, the laws in individual states and mainland territories are applicable only within those states and territories while influencing the jurisdiction of other states. InfoSec provides safety from unauthenticated and unauthorized access, modification or destruction of data, unauthorized inspection and recording of data. OFT is responsible from cushioning consumers against anti-competitive or illicit business behavior Office of Fair Trading 2012. It is imperative that you read and understand the limits of privacy and confidentiality before you start treatment.
Moreover, the process of counseling usually involves working through tough personal issues that can result in some emotional or psychological pain for the client. Attempting to resolve issues that brought clients to therapy in the first place may result in changes that were not originally intended. Being an IT manager, various actions can be taken to achieve this objective. In relation to The Competition Act 1998, two prohibitions can be separated, namely Chapter 1, which is concerned with discouraging any co-ordinated actions that exists between firms that subsequently leads to an anti-competitive. A no-waiver provision is usually included to extend the duration in which the parties can file a suit in the event of a Miscellaneous Other miscellaneous provisions that may be included in the confidentiality statement include: Jurisdiction The laws and courts that will handle any disputes. . Vice President Joe BidenThe White House1600 Pennsylvania Ave.